Security & Compliance
Local-first AI operations backed by cryptographic evidence, scoped authorization, and compliance-ready architecture.
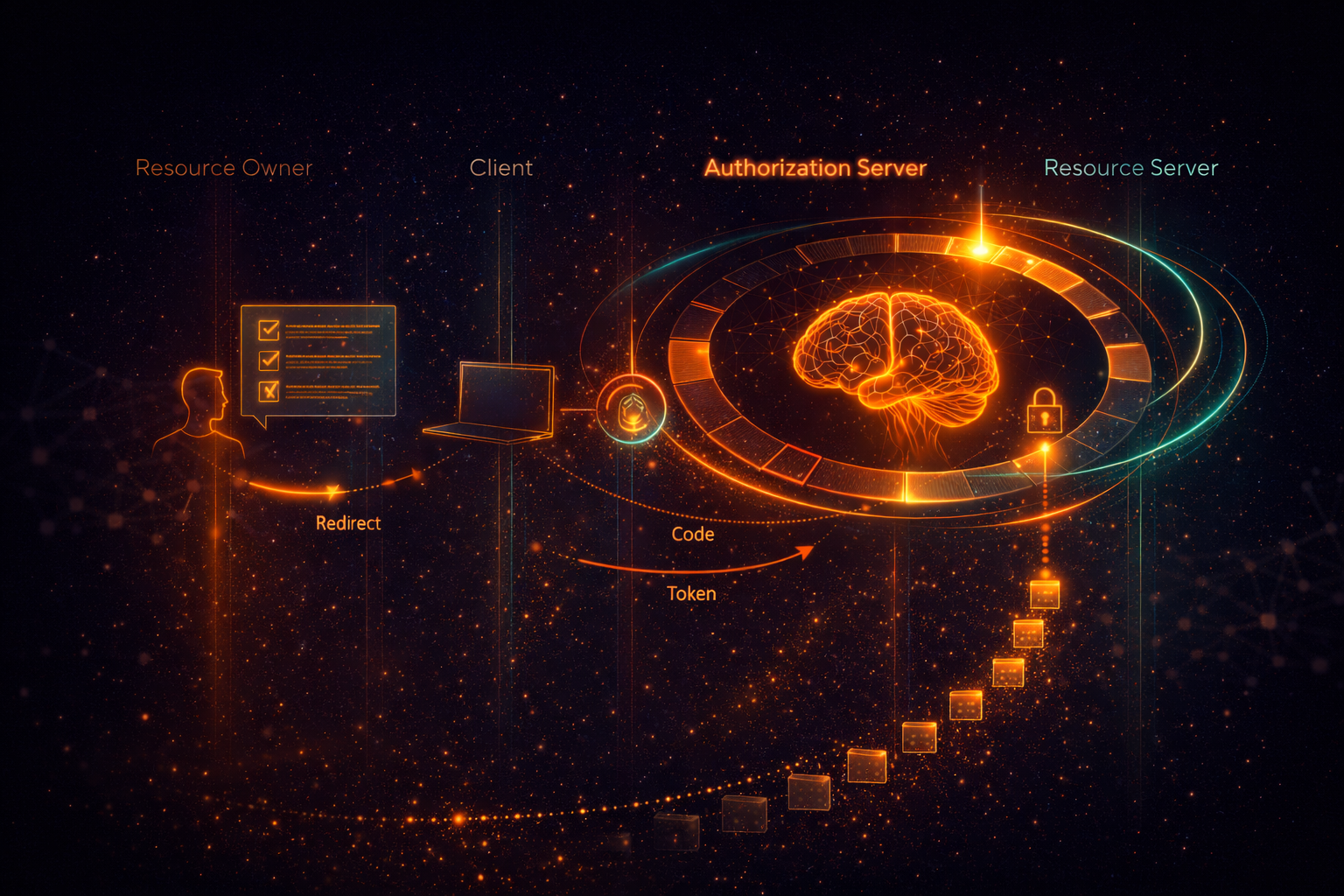
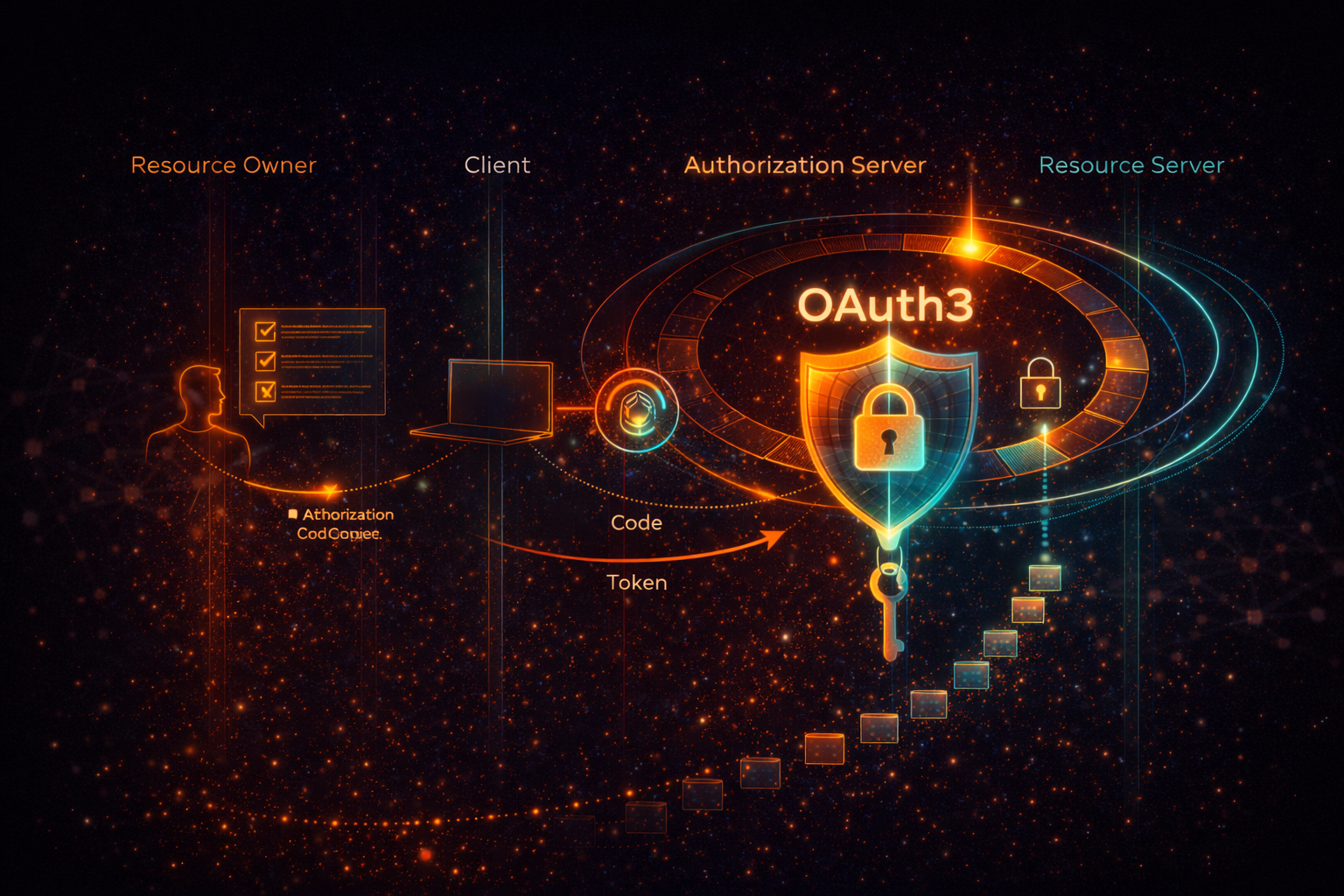
OAuth3 Scopes & Agent Authorization
Traditional API keys give agents broad, unlimited access. Solace uses OAuth3 to provide granular permissions. Each agent is issued a scoped token that defines exactly what actions it can perform, the duration of its permission, and the evidence it must collect. High-risk operations require explicit step-up approvals and are strictly governed by TTL (Time-To-Live) constraints.
AES-256-GCM Vault
Your credentials, API keys, and sensitive workflow data are encrypted at rest using AES-256-GCM. The encryption keys are managed securely, ensuring that Solace Browser acts on your behalf without exposing secrets in plaintext. Decryption happens only in memory at the exact moment an action requires credentials to proceed.
SHA-256 Hash Chains
Every critical operation, including e-signatures and agent actions, is logged in an immutable SHA-256 hash chain. Each new record hashes the previous record’s signature, creating a cryptographically verifiable trail. Any tampering breaks the mathematical chain, making modification evident and independently verifiable.
Local-First Execution & Zero Telemetry
Solace operates on a BYOK (Bring Your Own Key) model. Your LLM API keys never leave your machine. We collect zero workflow telemetry. Execution happens locally by default, ensuring your proprietary data remains entirely within your own security boundary. Cloud sync is optional.
FDA Part 11 & ALCOA+ Architected
Solace is architected to support regulatory workflows. Our evidence engine implements FDA 21 CFR Part 11 compliance patterns, meaning electronic signatures and audit trails support non-repudiation controls for medical, financial, and enterprise environments. Customer validation, SOPs, and deployment controls are required for full certification.
- Attributable: Every action is tied to an identity via secure authentication and OAuth3.
- Legible: Evidence is stored in readable JSON formats and visually reconstructable snapshots.
- Contemporaneous: Timestamps are securely captured at the exact moment of execution.
- Original: Artifacts are retained as untampered primary records.
- Accurate: Cryptographic signatures verify that no changes have occurred to the evidence string.
Report a Vulnerability
Emailsecurity@solaceagi.comwith reproduction steps, affected URL or build, impact assessment, and proof-of-concept details. Please do not access customer data, exfiltrate secrets, or perform destructive testing.
- Acknowledgement target:2 business days
- Status updates:every 5 business days for accepted reports
- Safe harbor:good-faith research within this policy will not trigger legal action
- Disclosure:coordinate public disclosure with Phuc Labs after remediation
Secure Your Workflows Today
Experience local-first AI automation with built-in cryptographic evidence, scoped authorization, and tamper-evident audit trails.
